Social Engineering: The Human Element How Does Social Engineering Work and to What Purpose? Chuck McGann. - ppt download
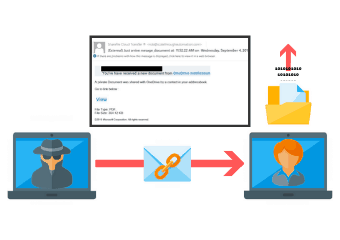
Be Smart and Be Secure with Social EngineeringBe Smart and Be Secure with Social Engineering | Bermartabat.com

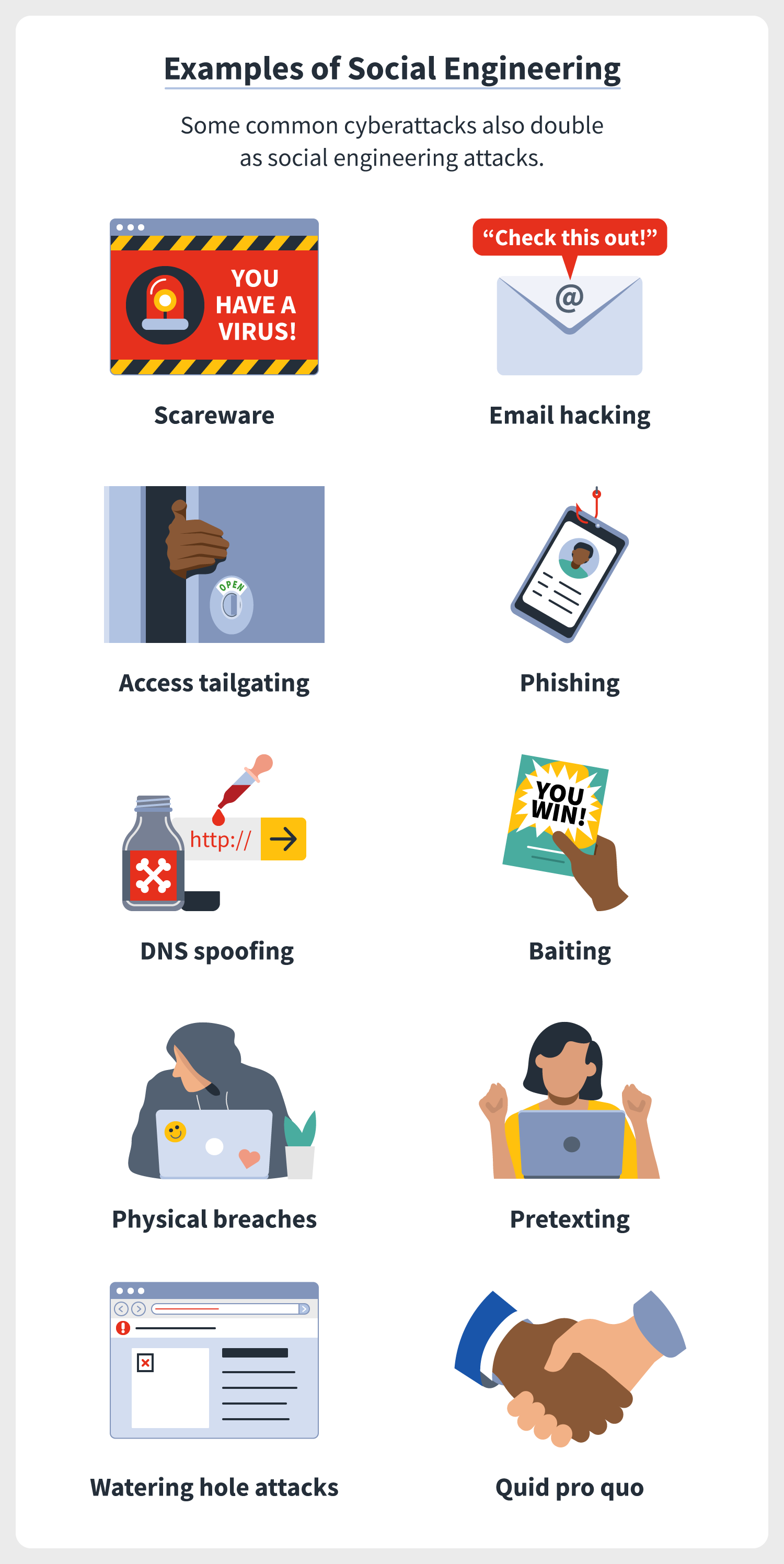
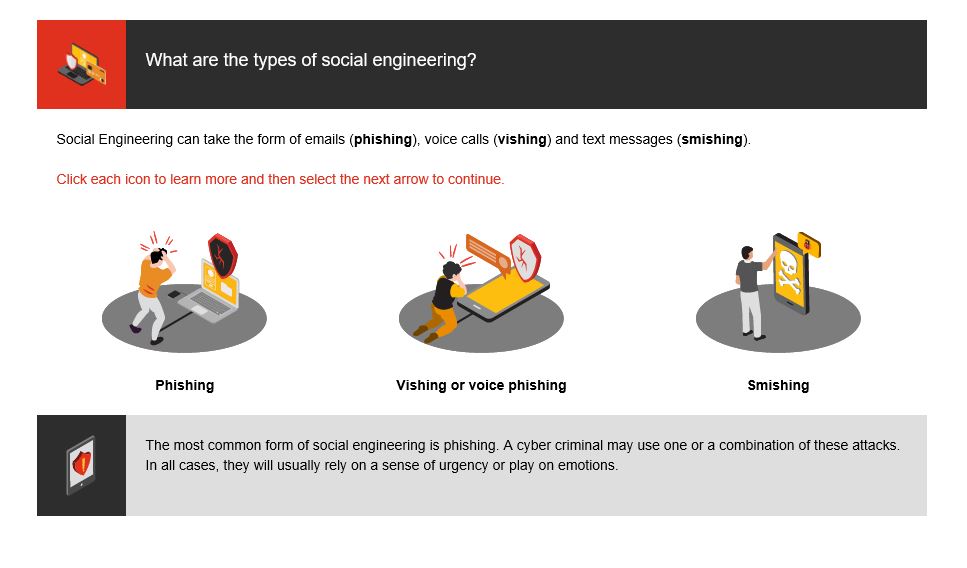
Social Engineering Attacks: A Look at Social Engineering Examples in Action - Hashed Out by The SSL Store™



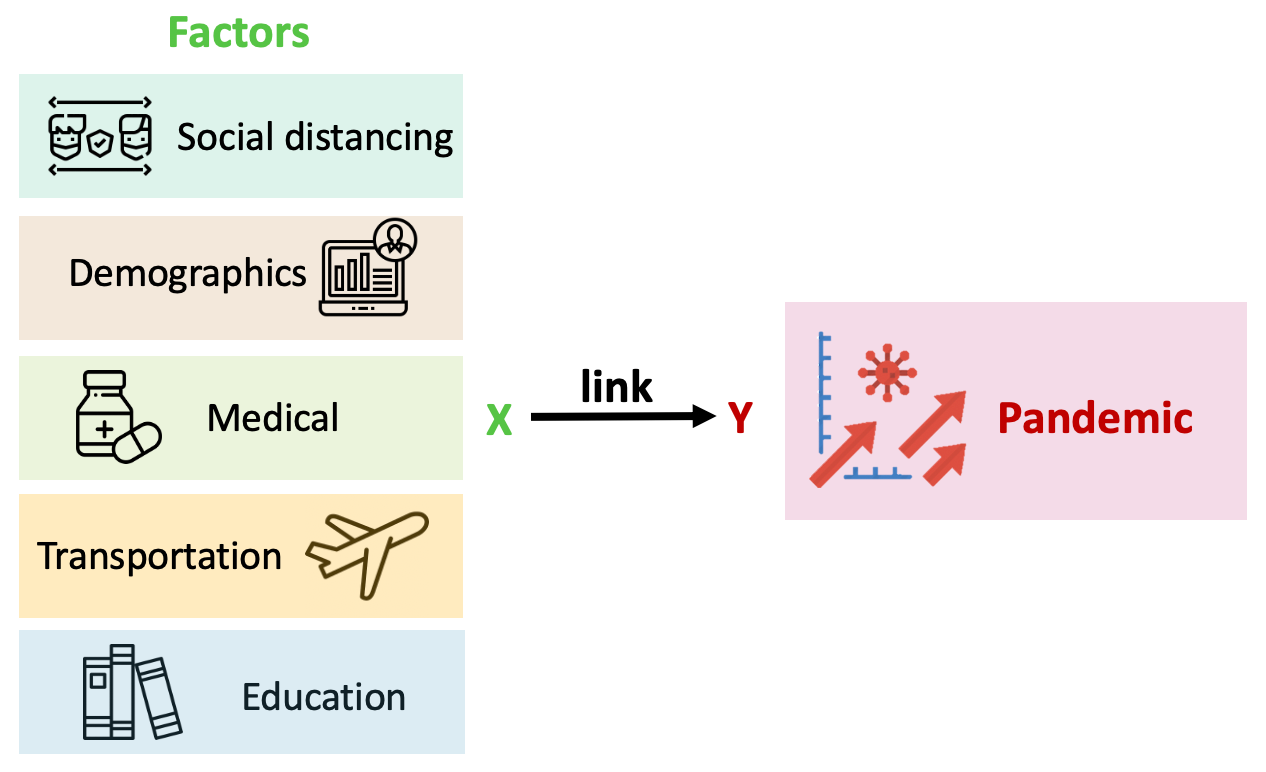
![PDF] Development of Methodical Social Engineering Taxonomy Project | Semantic Scholar PDF] Development of Methodical Social Engineering Taxonomy Project | Semantic Scholar](https://d3i71xaburhd42.cloudfront.net/d130cea7acdabe16ca592a7cdc09bca87cc2a6d1/19-Figure1-1.png)